Ransomware has fundamentally changed the backup conversation for UK businesses. It is no longer sufficient to simply have backups — you need backups that cannot be compromised, encrypted, or deleted by an attacker who has gained access to your network. Traditional backup approaches, where backup data sits on a network-connected storage device or in a cloud repository accessible via standard credentials, are increasingly vulnerable to sophisticated ransomware attacks that specifically target backup systems before encrypting production data.
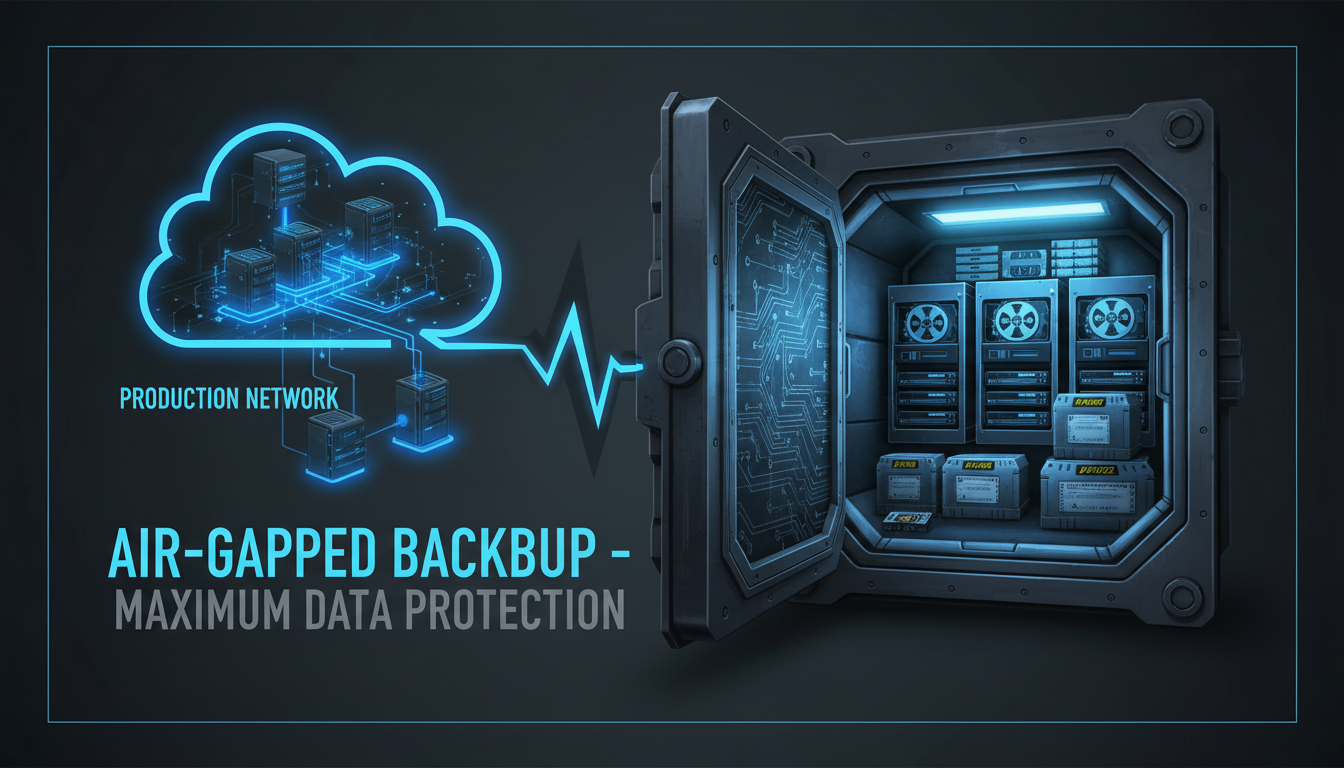
Air-gapped backups represent the ultimate line of defence against this threat. An air-gapped backup is a copy of your data that is physically or logically isolated from your network, making it impossible for ransomware — or any network-based attack — to reach, modify, or destroy the backup. If everything else fails — if your servers are encrypted, your cloud backups are compromised, and your online recovery options are exhausted — an air-gapped backup gives you a guaranteed path to recovery.
This guide explains what air-gapped backups are, why they have become essential for UK businesses, how different air-gap technologies work, and how to implement an air-gapped backup strategy that provides maximum protection without creating unmanageable operational complexity.
Why Traditional Backups Are No Longer Enough
The ransomware threat landscape has evolved dramatically since the early days of indiscriminate attacks. Modern ransomware operators — many of them organised criminal gangs operating out of Eastern Europe and Russia — conduct targeted, methodical attacks that can unfold over weeks or months. They gain initial access through phishing emails, vulnerable remote access points, or compromised credentials, then move laterally through the network, escalating privileges and mapping the environment before deploying ransomware.
Critically, these attackers now specifically seek out and compromise backup systems as part of their attack methodology. They look for backup servers, identify backup schedules, compromise backup administrator credentials, and either encrypt or delete backup data before deploying ransomware to production systems. The goal is to eliminate every recovery option, leaving the victim with no choice but to pay the ransom.
This means that a backup stored on a network-attached storage device, a backup server connected to your domain, or a cloud backup accessible via credentials that an attacker could steal, is no longer a guaranteed recovery path. If the attacker can reach your backup, they will destroy it. Only data that is physically or logically unreachable from the compromised network remains safe.
The National Cyber Security Centre (NCSC) explicitly recommends that UK organisations maintain an offline or air-gapped backup as part of their ransomware defence strategy. Their guidance states that organisations should "keep an offline backup of your data, in a location that is separate from your network and systems." The NCSC also recommends that this backup is tested regularly to ensure it can be used for recovery. For businesses seeking Cyber Essentials Plus certification, demonstrating a robust backup strategy including offline or air-gapped copies strengthens the overall security assessment.
What Is an Air-Gapped Backup?
An air-gapped backup is a copy of your data that is isolated from your network and systems by an "air gap" — a physical or logical separation that prevents any network-based access to the backup data. The term originates from military and government security practices, where classified systems are physically disconnected from all networks to prevent unauthorised access.
In the context of business data protection, air-gapping can be achieved through several methods, each offering different levels of isolation, convenience, and cost. The three primary approaches are physical air gaps (using removable media that is disconnected and stored separately), logical air gaps (using technology that makes backup data immutable and inaccessible to network-connected systems), and cloud-based immutable storage (using cloud features that prevent any modification or deletion of stored data, even by administrators).
Air-Gapped Backup: Protected
- Physically or logically isolated from network
- Cannot be encrypted by ransomware
- Cannot be deleted by compromised admin accounts
- Provides guaranteed recovery path
- Meets NCSC and Cyber Essentials requirements
- Survives total network compromise
- Independent of production infrastructure
- Time-locked retention prevents premature deletion
Network-Connected Backup: Vulnerable
- Accessible from the network via standard protocols
- Can be encrypted by ransomware alongside production data
- Admin credentials can be used to delete backups
- No recovery if attacker targets backup systems
- May not satisfy regulatory requirements
- Compromised when the network is compromised
- Depends on production infrastructure
- Backups can be silently corrupted over time
Air-Gap Technologies Compared
Understanding the different air-gap technologies helps you choose the approach that best fits your business requirements, budget, and operational capabilities. Each method has distinct advantages and trade-offs.
| Method | Isolation Level | Automation | Cost | Best For |
|---|---|---|---|---|
| Removable USB/HDD (rotated off-site) | Physical — highest | Manual rotation required | Low (£200-£500) | Very small businesses |
| RDX Cartridges | Physical — high | Semi-automated | Medium (£500-£2,000) | SMEs with structured processes |
| LTO Tape | Physical — highest | Automated with tape library | High (£3,000-£15,000) | Larger businesses, compliance-driven |
| Immutable Cloud Storage (S3 Object Lock) | Logical — high | Fully automated | Medium (per-GB pricing) | Cloud-first businesses |
| Veeam Hardened Repository | Logical — high | Fully automated | Medium-High | Virtualised environments |
| Datto / BCDR Appliance | Logical — high | Fully automated | High (subscription model) | MSP-managed environments |
Implementing a Physical Air Gap
A physical air gap provides the strongest isolation because the backup media is completely disconnected from all systems and networks when not actively being written to. The most common physical air-gap methods for UK businesses are rotating external drives and LTO tape.
For smaller UK businesses, a rotating set of external USB hard drives or RDX cartridges provides a simple and affordable physical air gap. The process works as follows: maintain at least three external drives in rotation. Each day (or each backup cycle), connect one drive to the backup server, run the backup, then disconnect the drive and store it in a secure location — ideally a fire-rated safe on-site and a secondary copy at an off-site location such as a bank safe deposit box or a director's home. The following day, use the next drive in the rotation. This ensures that even if one drive is connected during an attack, the other two drives are safely disconnected and available for recovery.
For larger organisations or those with more demanding compliance requirements, LTO tape remains the gold standard for physical air-gapped backup. Modern LTO-9 tapes store up to 18TB of native data (45TB compressed) per cartridge, with transfer speeds sufficient for enterprise backup windows. Tape libraries automate the backup process, and cartridges are physically removed and stored off-site for maximum protection. Many UK financial services firms, legal practices, and healthcare organisations use LTO tape specifically because it satisfies regulatory requirements for offline data protection.
Implementing a Logical Air Gap
A logical air gap uses technology rather than physical disconnection to isolate backup data. While not as absolute as a physical air gap, a properly implemented logical air gap provides strong protection against ransomware and is significantly easier to automate and manage.
The most common logical air-gap technologies for UK businesses include immutable cloud storage (such as AWS S3 Object Lock or Azure Immutable Blob Storage), which allows data to be written once and prevents any modification or deletion for a defined retention period. Even if an attacker compromises your AWS or Azure credentials, they cannot delete or modify data protected by immutability policies. The retention period is enforced at the platform level, making it immune to credential-based attacks.
Veeam's Hardened Linux Repository is another popular logical air-gap option for businesses with virtualised environments. This approach uses a dedicated Linux server configured with no SSH access and immutable backup flags, ensuring that backup data cannot be modified or deleted from the network. The server accepts backup data only through the Veeam backup engine and rejects all other access attempts.
The 3-2-1-1-0 Backup Rule
The traditional 3-2-1 backup rule (three copies, two media types, one off-site) has evolved to address the ransomware threat. The modern best practice for UK businesses is the 3-2-1-1-0 rule: three copies of your data, on two different media types, with one copy off-site, one copy air-gapped or immutable, and zero errors (verified through regular testing).
The addition of the air-gapped copy and the zero-errors requirement reflects the current threat landscape. The air-gapped copy ensures recovery even in the worst-case scenario, while the zero-errors requirement emphasises that untested backups are unreliable backups. A backup that has never been restored is a hope, not a strategy.
Testing Your Air-Gapped Backups
An air-gapped backup that has never been tested is a liability disguised as a safety net. Regular testing is essential to verify that backup data is complete, uncorrupted, and restorable within your recovery time objectives.
Conduct restore tests at least quarterly. For physical air-gapped media, this means connecting the backup drive or loading the tape, initiating a restore of representative data (a mixture of files, databases, and application data), and verifying that the restored data is complete and usable. For logical air-gap solutions, initiate a restore from the immutable storage to a test environment and verify data integrity.
Document the results of every test, including the time taken to restore, any errors encountered, and the actions taken to resolve them. This documentation serves dual purposes: it confirms that your backup strategy works, and it provides evidence for compliance audits and regulatory reviews. The ICO and other regulatory bodies look favourably on organisations that can demonstrate a tested and documented backup strategy.
Compliance and Regulatory Drivers for UK Businesses
Beyond the immediate ransomware protection benefits, air-gapped backups increasingly feature in UK regulatory and compliance frameworks. The Information Commissioner's Office (ICO) considers backup strategy as part of its assessment of whether an organisation has implemented appropriate technical and organisational measures under UK GDPR Article 32. Organisations that suffer a data breach and cannot demonstrate a robust, tested backup strategy — including offline or air-gapped copies — may face higher penalties and more critical regulatory scrutiny during incident investigations. The ICO's enforcement actions in recent years have consistently highlighted data recovery capability as a key factor in determining penalty severity.
For businesses operating in regulated sectors, the requirements are even more explicit. The Financial Conduct Authority (FCA) expects firms to maintain operational resilience, including the ability to recover critical data within defined tolerances. The Solicitors Regulation Authority (SRA) requires law firms to have robust data protection measures, and the ability to recover client files after a cyber incident is a fundamental expectation. Healthcare organisations processing NHS data must comply with the Data Security and Protection Toolkit (DSPT), which includes specific requirements around backup and recovery capabilities that air-gapped solutions directly address. These sector-specific obligations mean that air-gapped backups are not optional extras for regulated businesses — they are practical necessities for demonstrating compliance.
The Cyber Essentials Plus certification scheme, widely adopted across UK businesses and increasingly required for government contracts, evaluates backup practices as part of its assessment criteria. While Cyber Essentials does not explicitly mandate air-gapped backups, demonstrating an air-gapped or immutable backup strategy significantly strengthens your certification position and demonstrates mature security practices to clients and partners who review your certification status. Many organisations pursuing ISO 27001 certification also find that air-gapped backups satisfy multiple controls within Annex A, particularly those relating to information backup (A.12.3) and protection against malware (A.12.2). The combination of Cyber Essentials Plus and ISO 27001 is becoming a standard expectation for UK businesses bidding on government and enterprise contracts.
Insurance providers are also driving adoption of air-gapped backup strategies across the UK market. Cyber insurance underwriters increasingly ask about backup isolation during the application and renewal process. Businesses that can demonstrate air-gapped or immutable backup practices often receive more favourable premium terms, while those relying solely on network-connected backups may face higher premiums, coverage exclusions, or outright refusal of ransomware coverage. Several major UK cyber insurers now list offline or immutable backup as a prerequisite for ransomware coverage, making air-gapped backup not just a technical best practice but a commercial necessity for maintaining affordable cyber insurance. The cost savings on insurance premiums alone can offset a significant portion of the investment in air-gapped backup infrastructure.
Common Mistakes When Implementing Air-Gapped Backups
Even organisations that recognise the need for air-gapped backups often make implementation errors that undermine the effectiveness of their strategy. Understanding these common pitfalls helps you avoid them and ensures your air-gapped backups deliver genuine protection when you need them most.
The most frequent mistake is treating air-gapped backup as a one-time project rather than an ongoing operational discipline. Setting up an air-gapped backup rotation is only the beginning — without regular testing, documented procedures for staff turnover, and periodic reviews of backup scope and retention policies, the air-gapped backup gradually drifts into unreliability. Drives sit in safes untested for months. New servers and applications get added to the environment but never included in the air-gapped backup schedule. Staff who understood the rotation process leave the business, and their replacements are never properly trained on the procedures. The result is an air-gapped backup that exists in name only, providing false confidence rather than genuine protection.
Another common error is insufficient scope in the air-gapped backup strategy. Businesses often air-gap their server backups but overlook critical data stored in cloud SaaS applications, email archives, or specialist line-of-business systems. A comprehensive air-gapped backup strategy must account for all critical data repositories, not just on-premises file servers. This includes Microsoft 365 data (which Microsoft does not back up or air-gap on your behalf), cloud-hosted databases, configuration data for network equipment and security devices, and any data held in specialist industry applications that your business depends on for daily operations. A backup strategy that protects your file server but ignores your Microsoft 365 mailboxes and SharePoint data leaves a massive gap in your recovery capability.
Businesses also frequently underestimate the recovery process itself. Having air-gapped backup data is necessary but not sufficient — you also need the infrastructure, documentation, and trained staff to execute a full recovery under pressure. This means maintaining up-to-date documentation of recovery procedures, ensuring you have access to the hardware or cloud resources needed to restore systems, and verifying that application licence keys and configuration details are accessible independently of the compromised environment. A tabletop recovery exercise, conducted at least annually, reveals gaps in your recovery capability before a real incident forces you to discover them under extreme time pressure and stress. Many UK businesses that invested properly in air-gapped backups still experienced extended downtime during recovery because they had not practised or documented the restoration process itself.
Protect Your Business with Air-Gapped Backups
Cloudswitched designs and implements air-gapped backup solutions for UK businesses of all sizes. From rotating physical media for small offices to enterprise-grade immutable cloud storage and LTO tape libraries, we tailor the solution to your data volumes, compliance requirements, and recovery objectives.