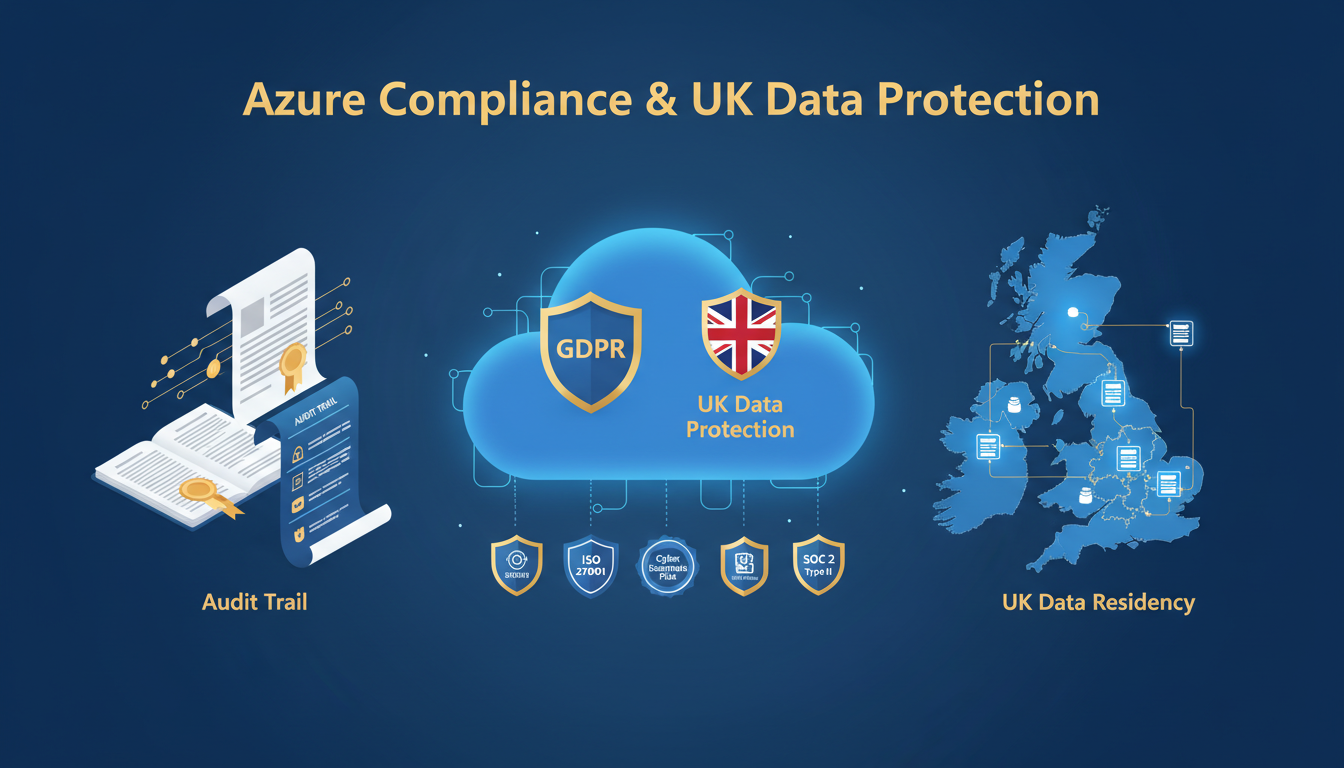
For UK businesses moving workloads to Microsoft Azure, compliance with data protection legislation is not optional — it is a fundamental requirement that must be addressed from the very beginning of any cloud adoption journey. The UK General Data Protection Regulation (UK GDPR), the Data Protection Act 2018, and sector-specific regulations impose strict requirements on how personal data is collected, processed, stored, and transferred.
Microsoft Azure provides extensive compliance capabilities and certifications, but using Azure does not automatically make your organisation compliant. Compliance is a shared responsibility: Microsoft ensures that the Azure platform meets the required standards, while your organisation is responsible for how you configure and use Azure services, what data you store, and how you manage access and security.
This guide examines how Azure supports UK data protection compliance, what your organisation needs to do to meet its obligations, and the specific Azure features and configurations that help maintain a compliant environment.
The UK Data Protection Landscape
Since the United Kingdom's departure from the European Union, UK data protection is governed by the UK GDPR — a UK-specific version of the EU GDPR retained in domestic law — and the Data Protection Act 2018. The Information Commissioner's Office (ICO) is the supervisory authority responsible for enforcing these regulations.
The core principles remain the same as the EU GDPR: lawfulness, fairness, and transparency; purpose limitation; data minimisation; accuracy; storage limitation; integrity and confidentiality; and accountability. For organisations using cloud services like Azure, the integrity and confidentiality principle and the accountability principle are particularly relevant, as they require organisations to implement appropriate technical and organisational measures to protect personal data and to be able to demonstrate compliance.
In practice, this means that when you store personal data in Azure, you must ensure that the data is encrypted, access-controlled, auditable, and that you know exactly where it is geographically located. You must have a lawful basis for processing, you must be able to respond to data subject access requests (DSARs), and you must be prepared to notify the ICO within 72 hours if a personal data breach occurs.
Microsoft operates on a shared responsibility model for compliance. Microsoft is responsible for the security and compliance of the Azure platform itself — the physical data centres, the host operating systems, the network infrastructure, and the virtualisation layer. Your organisation is responsible for everything you deploy on top of that — your virtual machines, your data, your access controls, your applications, and your encryption configuration. Selecting Azure as your cloud provider is a strong foundation, but it is only the foundation. How you build on it determines whether you are truly compliant.
Understanding the broader regulatory context is equally important. Beyond the UK GDPR and the Data Protection Act 2018, many UK organisations must also comply with sector-specific regulations that impose additional requirements on cloud deployments. Financial services firms are subject to oversight from the Financial Conduct Authority (FCA) and the Prudential Regulation Authority (PRA), both of which have published specific guidance on cloud outsourcing and operational resilience. Healthcare organisations handling NHS data must comply with the Data Security and Protection Toolkit (DSPT) and relevant NHS Digital standards. Public sector bodies may need to meet the requirements of the Government Security Classifications policy and the National Cyber Security Centre (NCSC) Cloud Security Principles. Azure's extensive compliance certifications cover many of these frameworks, but your organisation must still demonstrate that its specific Azure configuration meets the requirements of each applicable regulation.
Azure UK Data Residency
One of the most important compliance considerations for UK organisations is data residency — knowing exactly where your data is physically stored. Many UK businesses and regulators require that personal data remains within UK borders, or at minimum within jurisdictions that provide adequate data protection.
Microsoft Azure operates two data centre regions within the United Kingdom: UK South (London) and UK West (Cardiff). By selecting these regions for your Azure resources, you can ensure that your data is stored and processed within the UK. This addresses data residency requirements for most UK compliance scenarios and eliminates concerns about international data transfers.
When configuring Azure resources, it is essential to explicitly select UK regions for every service that stores or processes personal data. Some Azure services may default to non-UK regions, and some features may only be available in certain regions. Your cloud architect or IT provider should verify the region configuration for every resource as part of the deployment process.
For services that require data replication for resilience — such as geo-redundant storage — you should configure replication to use the paired UK regions (UK South paired with UK West) rather than cross-border replication. This ensures that even your backup copies remain within UK borders.
| Azure Region | Location | Paired Region | Use Case |
|---|---|---|---|
| UK South | London | UK West | Primary workloads for UK data residency |
| UK West | Cardiff | UK South | Disaster recovery and geo-redundancy |
| North Europe | Ireland | West Europe | EU adequacy — suitable for non-UK personal data |
| West Europe | Netherlands | North Europe | EU adequacy — suitable for non-UK personal data |
Encryption: Protecting Data at Rest and in Transit
UK GDPR requires appropriate technical measures to protect personal data, and encryption is one of the most fundamental. Azure provides comprehensive encryption capabilities, but understanding the options and configuring them correctly is your responsibility.
Encryption at rest: Azure encrypts all data at rest by default using 256-bit AES encryption through Azure Storage Service Encryption (SSE). This applies to Azure Blob Storage, Azure Files, Azure Managed Disks, and other storage services. For most UK compliance scenarios, Microsoft-managed encryption keys provide adequate protection. However, for organisations with enhanced requirements, Azure supports customer-managed keys (CMK) stored in Azure Key Vault, giving you full control over the encryption keys.
Encryption in transit: All data moving between Azure services and your users should be encrypted using TLS 1.2 or higher. Azure services enforce TLS encryption by default for management plane operations, but you must ensure that your applications also use TLS for data plane operations. Verify that older TLS versions (1.0 and 1.1) are disabled across your Azure resources, as these protocols have known vulnerabilities.
Azure Disk Encryption: For virtual machines running in Azure, Azure Disk Encryption uses BitLocker (Windows) or dm-crypt (Linux) to encrypt OS and data disks. This provides volume-level encryption that protects data even if the underlying storage is accessed outside the context of your virtual machine.
It is also worth considering the role of Azure Confidential Computing for workloads that involve particularly sensitive personal data. Confidential Computing uses hardware-based trusted execution environments (TEEs) to encrypt data whilst it is being processed — not just at rest or in transit. This means that even Azure administrators and the underlying hypervisor cannot access the data during computation. For organisations processing large volumes of sensitive personal data — such as healthcare records, financial information, or biometric data — Confidential Computing provides an additional layer of protection that goes beyond standard encryption. Azure offers confidential virtual machines and confidential containers that support this capability across both Intel SGX and AMD SEV-SNP hardware. Whilst not required by UK GDPR in all cases, Confidential Computing can demonstrate that your organisation has implemented state-of-the-art technical measures, which is a strong position to hold during any regulatory assessment.
Identity and Access Management
Controlling who can access personal data in your Azure environment is a core compliance requirement. Azure Active Directory (now Microsoft Entra ID) provides the identity and access management framework, but it must be configured correctly to meet UK GDPR requirements.
Implement the principle of least privilege across your Azure environment. Every user, service account, and application should have only the minimum permissions necessary to perform their function. Use Azure Role-Based Access Control (RBAC) to assign permissions at the appropriate scope — subscription, resource group, or individual resource level. Avoid assigning broad permissions such as Owner or Contributor at the subscription level unless absolutely necessary.
Enable multi-factor authentication (MFA) for all users accessing Azure resources. The NCSC recommends MFA as one of the most effective security controls, and the ICO considers the absence of MFA when assessing whether an organisation has implemented appropriate technical measures. Use Conditional Access policies to enforce MFA based on risk signals such as sign-in location, device compliance, and real-time risk detection.
Implement Privileged Identity Management (PIM) for administrative access. PIM provides just-in-time (JIT) access elevation, requiring administrators to explicitly activate their elevated permissions for a limited time period with justification and approval. This reduces the window of exposure for privileged accounts and provides a complete audit trail of administrative actions.
Auditing, Logging, and Monitoring
The accountability principle of UK GDPR requires organisations to demonstrate compliance — not just be compliant, but be able to prove it. Azure provides extensive logging and auditing capabilities that, when properly configured, create a comprehensive record of all activity in your environment.
Enable Azure Activity Logs for all subscriptions. These logs record every management plane operation — resource creation, modification, and deletion — providing an audit trail of who did what, when, and from where. Activity logs are retained for 90 days by default but should be exported to a Log Analytics workspace or Azure Storage for long-term retention.
Configure Azure Monitor and Microsoft Defender for Cloud to provide continuous security monitoring. Defender for Cloud assesses your Azure configuration against security benchmarks and compliance frameworks, highlighting misconfigurations and vulnerabilities. It also provides threat detection capabilities, alerting you to suspicious activity that might indicate a data breach.
For GDPR-specific compliance tracking, use the Microsoft Purview Compliance Manager. This tool provides a compliance score based on your current configuration, identifies gaps, and provides improvement actions with step-by-step guidance. It includes assessments for UK GDPR, ISO 27001, Cyber Essentials, and other relevant frameworks.
Organisations should also consider the importance of data classification as part of their Azure compliance strategy. Microsoft Purview Information Protection allows you to classify and label data based on its sensitivity — from public information through to highly confidential personal data. Once classified, sensitivity labels can automatically apply encryption, restrict access, add watermarks, and prevent data from being shared externally. For UK GDPR compliance, data classification helps ensure that personal data receives appropriate protection based on its sensitivity and the risk associated with its processing. A robust classification scheme also makes it significantly easier to respond to data subject requests, as you can quickly identify where personal data resides and what protections are applied to it. Implementing data classification early in your Azure adoption journey avoids the considerably more difficult task of retrospectively classifying data across an established environment.
Data Subject Rights and Azure
Under UK GDPR, individuals (data subjects) have specific rights regarding their personal data, including the right of access, the right to rectification, the right to erasure, and the right to data portability. Your Azure environment must support your ability to fulfil these requests within the required one-month timeframe.
For subject access requests (DSARs), you need the ability to search across all your Azure data stores — databases, blob storage, virtual machine disks, and application logs — to identify all personal data relating to a specific individual. Azure Purview (now Microsoft Purview) can help by cataloguing and classifying data across your estate, making it easier to locate personal data when a request is received.
For erasure requests (the right to be forgotten), you need the ability to identify and delete all instances of an individual's personal data across your Azure environment, including backups and archived copies. This can be technically challenging, particularly for data that has been replicated or backed up. Ensure your data architecture supports targeted deletion, and document any technical limitations that might delay erasure of backup copies.
Beyond the technical implementation of these rights, organisations must also establish clear internal processes and assign responsibilities for handling data subject requests. Designate a specific team or individual to receive and triage incoming requests, and establish service-level agreements for each stage of the process — from initial acknowledgement through to completion. Azure's data management capabilities provide the technical foundation, but without well-defined processes and trained staff, even the most sophisticated tooling will fall short of regulatory expectations. Regular training for all staff who may receive or handle DSARs is essential, and periodic test exercises — where you simulate receiving a complex DSAR and trace it through your entire process — help identify gaps before they become problems during a genuine request.
Azure Compliance Best Practices
- Deploy all UK personal data to UK South/UK West regions
- Enable encryption at rest and in transit for all services
- Enforce MFA and Conditional Access for all users
- Implement RBAC with least privilege principles
- Enable Azure Activity Logs with long-term retention
- Configure Microsoft Defender for Cloud
- Use Compliance Manager to track GDPR adherence
- Document data processing activities and legal bases
Common Compliance Mistakes
- Deploying resources to non-UK regions by default
- Relying solely on Microsoft's platform encryption
- Leaving MFA optional for some users or admins
- Assigning over-privileged roles at subscription level
- Not retaining audit logs beyond default periods
- Ignoring security recommendations from Defender
- Assuming Azure compliance equals organisational compliance
- No documented data processing impact assessments
Assessing your organisation's Azure compliance readiness requires evaluating several key dimensions. The following metrics represent the areas most commonly scrutinised during ICO investigations and compliance audits. Achieving high scores across all dimensions significantly reduces the risk of regulatory penalties and demonstrates a mature approach to data protection in the cloud.
Preparing for ICO Investigations
If the ICO investigates your organisation — whether following a data breach, a complaint, or a routine audit — you need to be able to demonstrate that you have implemented appropriate technical and organisational measures. Azure provides the tools to build this evidence, but you need to ensure they are configured and that the evidence is accessible.
Maintain a Record of Processing Activities (ROPA) that includes details of the personal data stored in Azure, the Azure regions used, the security measures applied, and the legal basis for each processing activity. This is a mandatory requirement under Article 30 of UK GDPR and is one of the first documents the ICO will request during an investigation.
Ensure you can demonstrate your security configuration at any point in time, not just the current state. Export Azure Policy compliance reports, Defender for Cloud security scores, and Compliance Manager assessments on a monthly basis and retain them. If a breach occurred three months ago and the ICO investigates today, you need to show what your security posture was at the time of the breach, not what it is now.
Have a tested incident response plan that specifically covers personal data breaches in Azure. The plan should include how breaches are detected, how the scope is assessed, how affected individuals are notified, and how the ICO notification is prepared and submitted within the 72-hour deadline. Test this plan at least annually with a tabletop exercise involving your IT team, data protection officer, and senior management.
Need Help with Azure Compliance?
Cloudswitched helps UK businesses design, deploy, and manage Azure environments that meet UK GDPR and data protection requirements. From initial architecture and data residency planning through to ongoing compliance monitoring and incident response preparation, we ensure your Azure environment supports your regulatory obligations. Contact us to discuss your compliance needs.
GET IN TOUCH